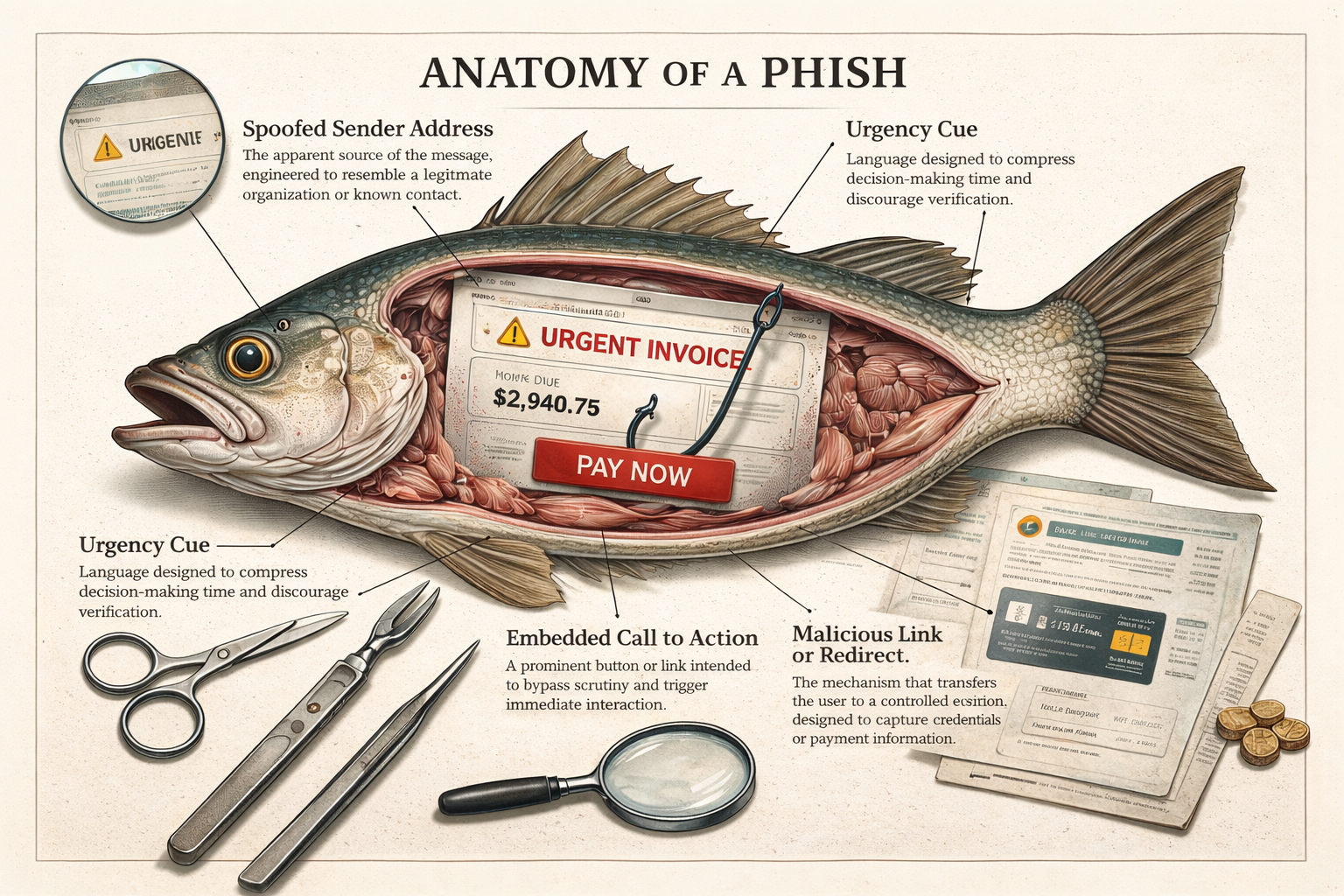
The Anatomy of a Phish
Nearly every successful phishing attempt follows the same internal anatomy.
Most phishing attempts fail.
This is not because they are unsophisticated, but because they are indifferent to precision. They are sent at scale. They assume loss. They rely on volume rather than accuracy.
What matters, however, is not the failure rate.
It is the consistency of the structure.
Nearly every successful phishing attempt follows the same internal anatomy. The surface details change. The underlying components do not.
This article dissects those components.
Spoofed Sender Address
The first layer of a phishing message is the sender.
This is rarely a random address. It is engineered to resemble a legitimate organization or known contact, often by substituting visually similar characters or domains. The goal is not perfect imitation, but plausibility at a glance.
Recipients do not verify senders carefully. They verify familiarity. If the name resembles something already trusted, scrutiny drops.
This is why spoofing targets recognition, not accuracy.
Urgency Cue
Phishing messages almost always compress time.
Language such as urgent, final notice, or immediate action required is used to narrow the recipient’s decision window. T his is not accidental. Verification takes time. Panic does not.
The message is designed to move the recipient from reading to acting without reflection.
Urgency does not need to be extreme. Mild pressure is often more effective than alarm. The goal is not fear, but haste.
Invoice or Payment Pretext
Many phishing attempts present themselves as routine financial interactions: invoices, account adjustments, shipping charges, or service renewals.
This framing accomplishes two things.
First, it normalizes the request. Payments are ordinary. People process them habitually.
Second, it shifts the recipient into compliance mode. The question becomes how to resolve this, not whether it is legitimate.
The pretext does not need to be believable in detail. It needs to be familiar in form.
Embedded Call to Action
The most important visual element in a phishing message is the call to action.
This is often a button or prominent link labeled with imperative language: Pay Now, Verify Account, Review Invoice.
The design isolates this element visually. Bright colors. Clear contrast. Central placement.
The call to action is not persuasive. It is directional.
It tells the recipient what to do next.
Malicious Link or Redirect
The call to action leads to the payload delivery mechanism.
This may be a credential harvesting page, a payment portal, or a redirect to a controlled site designed to mimic a legitimate service.
The page does not need to function fully. It needs to capture information once.
Phishing pages are disposable. They are created, used, abandoned, and replaced quickly.
Longevity is not a goal.
Request for Sensitive Information
At the core of the phish is the ask.
Usernames. Passwords. One-time codes. Credit card numbers. Bank details.
The request is framed as necessary to resolve the fabricated issue. The language emphasizes completion, not risk.
The recipient is made to feel responsible for finishing the process.
This is the moment of extraction.
Minor Grammatical Errors
Many phishing messages contain small mistakes.
These are often misinterpreted as incompetence. In practice, they serve a filtering function.
Recipients who dismiss the message due to obvious errors are unlikely to comply anyway. Those who proceed despite imperfections are more susceptible to extraction.
Precision is not required. Acceptability is.
Visual Legitimacy Markers
Logos, formatting, and document structure are used to anchor trust.
These elements are not examined closely. They are processed peripherally.
The goal is not deception through detail, but reassurance through familiarity.
If it looks right, it is treated as right.
Contextual Plausibility Layer
More advanced phishing attempts incorporate contextual information.
Job titles. Recent transactions. Company names. Publicly available data.
This personalization increases relevance and suppresses doubt.
The recipient feels targeted, not broadcast to.
Which increases compliance.
Payload
The final objective of the phishing attempt is extraction.
Money. Credentials. Access.
Everything else is scaffolding.
Once the payload is delivered, the message has served its purpose.
Conclusion
Phishing succeeds not because people are careless, but because the system is optimized against reflection.
Each component of the phish is designed to move the recipient forward without pause.
Recognition replaces verification. Urgency replaces judgment. Completion replaces caution.
Understanding the anatomy does not eliminate risk.
But it does restore agency.
Scams rely on opacity. Analysis removes it.
This is how the mechanism works.